We’ve had two significant server vulnerabilities disclosed this week, and both warrant immediate attention from anyone running Linux servers or cPanel-based hosting.
What’s Been Disclosed
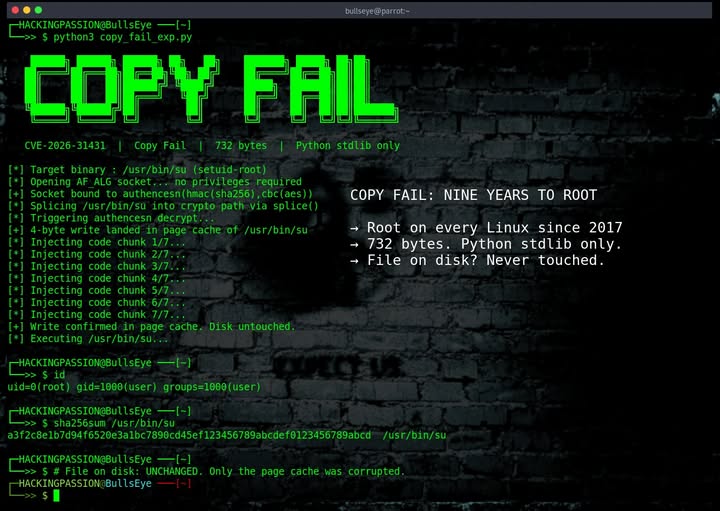
CVE-2026-31431 (“Copy Fail”) A flaw in the Linux kernel that could allow a local user to gain unauthorized root access. While it requires local access to exploit, on shared hosting environments or any server with multiple user accounts, this is a serious privilege escalation risk.
CVE-2026-41940 – A critical authentication bypass vulnerability in WHM/cPanel that could allow remote attackers to gain administrative access. This one is particularly nasty because it’s remotely exploitable, no prior access required.
Why This Matters
Most hosting environments in Ireland (and globally) run some flavour of Linux, and a huge portion of shared and reseller hosting sits on top of cPanel/WHM. That means these two CVEs together cover a substantial slice of the web hosting world.
If you manage your own server, VPS, or dedicated box, these are on you to patch. If you’re on managed hosting with us at WebWorld, we’ve already taken care of it across our infrastructure.
Are You Vulnerable to Copy Fail?
To make life easier, we’ve put together a free tool that lets you check whether your domain is running on a server that’s still exposed to the Copy Fail bug:
🔗 https://www.checkdomain.ie/copyfail/
Just enter your domain and we’ll do the rest. No login, no signup just a quick check.
How to Fix Them
For Copy Fail (CVE-2026-31431):
Update your Linux kernel to the latest patched version. On most distributions, that’s:Copy
# Debian/Ubuntu
sudo apt update && sudo apt upgrade -y
sudo reboot
# RHEL/CentOS/AlmaLinux/Rocky
sudo dnf update -y
sudo reboot
A reboot is required for the new kernel to take effect.
For the cPanel/WHM bug (CVE-2026-41940):
Simply update cPanel to the latest version. If you’ve got automatic updates enabled, you may already be patched, but it’s worth logging in and double-checking. You can run:Copy
/scripts/upcp --force
…from the command line as root to force an update immediately.
Need a Hand?
If you’re not sure whether you’re vulnerable, or you’d rather someone else handle the patching, get in touch. We can audit your server, apply the fixes, and verify everything’s locked down properly.
